Definition
It can be defined as a threat to any element or action capable of undermining the security of the information.Threats arise from the existence of vulnerabilities, that is, a threat can only exist if a vulnerability exists that can be exploited, regardless of whether the security of a computer system is compromised or not.
In recent years the increase in intentional threats is due to the lack of awareness of users in the use of technology, the increase in social engineering techniques, the lack of training and the increasing profitability of cyber attacks .
Knowing the types of threats.
The threats can be classified into two types:
Intentional, in the event that deliberate attempts are made to produce damage (for example, the theft of information by applying the trashing technique, the propagation of malicious code and social engineering techniques).
Unintentional, where there are actions or omissions of actions that while not seeking to exploit a vulnerability, put information assets at risk and may cause harm (for example, threats related to natural phenomena).
How to act
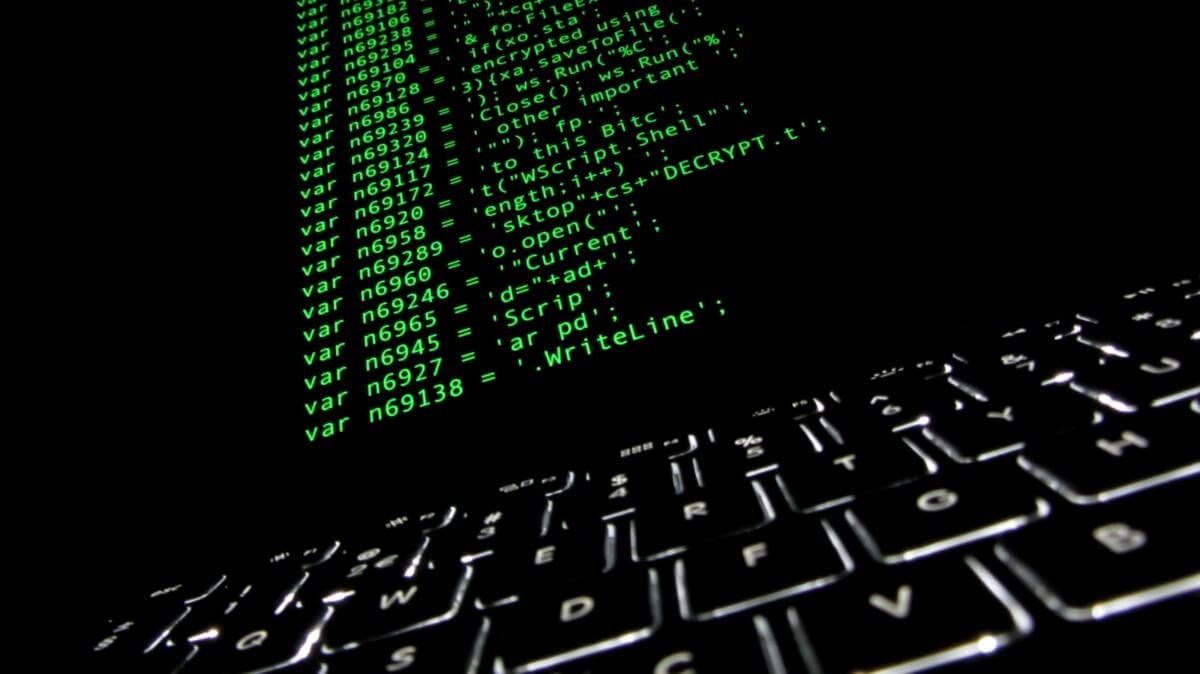
The presence of a threat is a warning that damage to some information asset may be imminent, or that the damage is occurring or has already occurred. Therefore, it should always be reported as an information security incident. ÂIn the security of a computer or some technological device, threats to those that affect the functioning of the systems must be considered. Some threats of this type are such as spyware, trojans, worms, even hackers, etc.
These threats are divided into 2 types:
Internal threats
This type of computer threats are, generally, more severe than all those that may come from abroad since users know the network and know how it works, have some level of access to the network, IPS and Firewalls are ineffective mechanisms in internal threats; so if someone inside a company wanted to make an attack the result would be severe.
External threats
They are those threats that originate from outside the network. By not having accurate information of the internal network of the company, the attacker has to take certain steps to know what is in it and find a way to attack it. The good news in this type of computer threats is that they can be avoided from within the company if you have the correct security measures.
Among the external computer threats includes:
Computer virus
It is a program that is automatically copied and that is intended to alter the normal functioning of the computer, without the user's permission. Viruses are programs that replicate and run on their own, usually replacing executable files with others infected with the virus code.
Worms
A worm is a computer virus that has the property of duplicating itself. Worms use the automatic parts of an operating system that are generally invisible to the user.
Spyware
The spyware is an application that collects valuable information from a person or organization without your knowledge.
Trojans
It is called Trojan, a malicious program that can be hosted on computers and allow access to external users, through a local network or the Internet, to collect information or control the computer remotely.
Hacker
A hacker is an alien user who enters into your computer with intentions to steal information and cause damage (such as spyware). The difference between a spyware and a hacker is that, in the second case, we are talking about a person who, through their knowledge, breaks the barriers that come in their way to enter a site or a computer.
We hope this information has been useful and you can know more about what can infect your computer or your mobile devices.
1553787120